Phishing stands as one of the most widely used cybercrime tactics right now. Phishing can be worryingly easy to carry out and can result in device infection and the theft of highly sensitive data. What’s more, almost everyone is at risk of falling victim to a phishing attack. But what actually is it? How does phishing work? And can you steer clear of it?
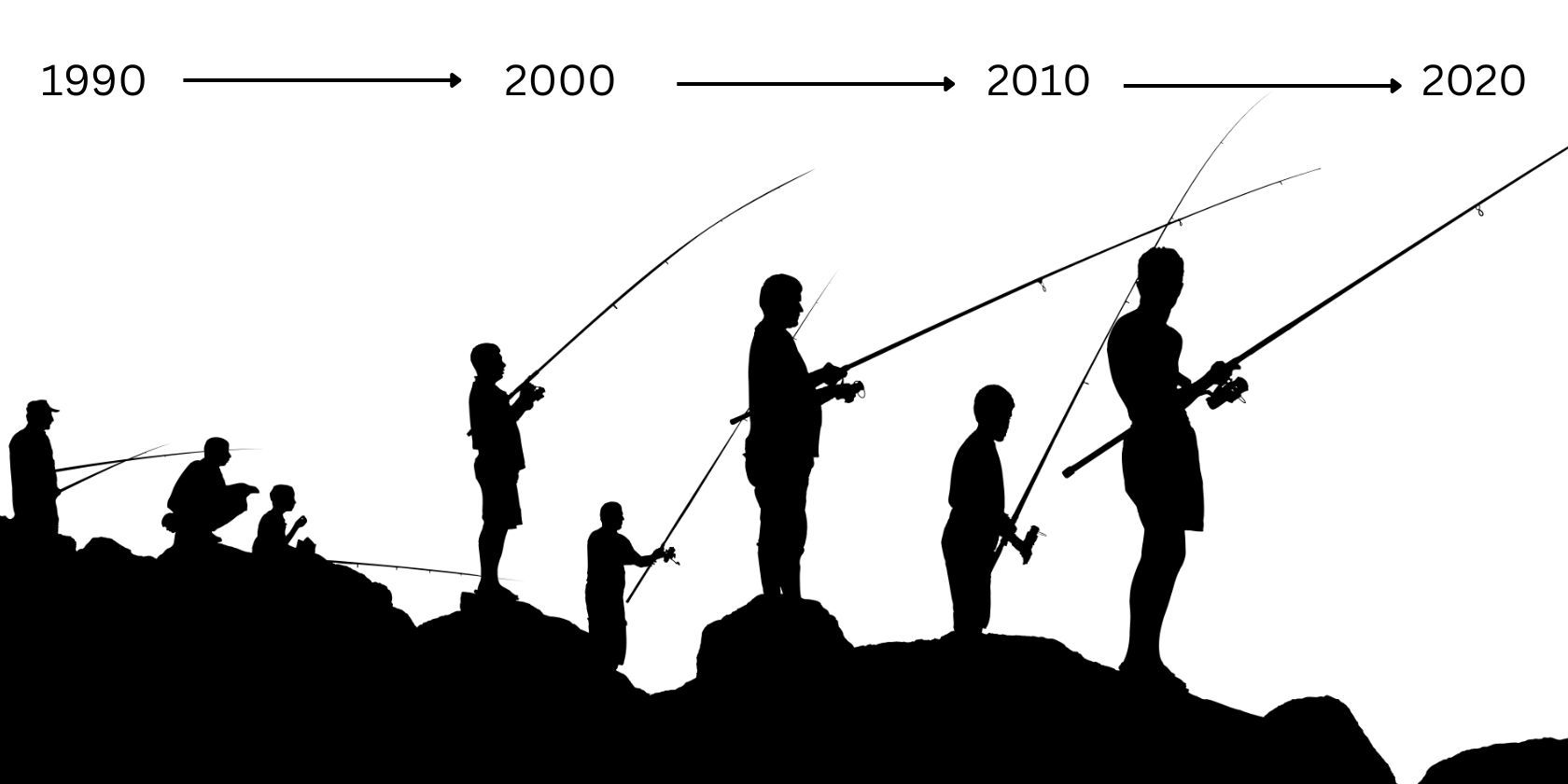
The History of Phishing
The act of phishing can be traced back to the mid-1990s when computers looked and worked very differently from those we use today. During this time, AOL (America Online), a popular American dial-up service, was the internet provider of choice for many. This made it a key target for phishers, who chose to impersonate AOL staff in order to steal valuable login information from victims.
Five years later, over 50 million computers became infected with something known as the Love Bug. This was a virus that spread among devices via social engineering. As the name suggests, this ploy relied on the lure of love to swindle victims. Targets would receive an email with an attachment that the sender claimed was a love letter. Curious individuals chose to open this attachment but did not realize that they were giving way to a dangerous scam.
The Love Bug virus would replicate itself in order to spread, making it a kind of computer worm. It was also an accelerated version of a previous bug created by the perpetrator, which was capable of stealing passwords. This new version of the…